News
Another Wide-Open Amazon S3 Bucket Exposes Verizon Customer Account Data
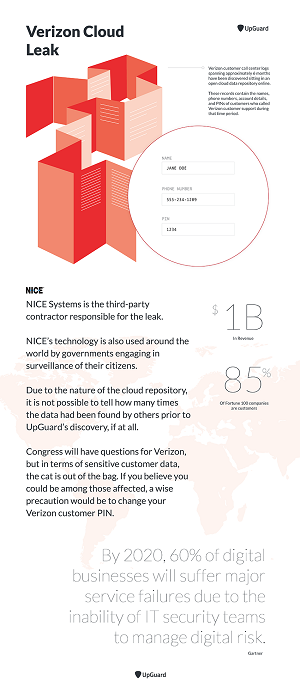
Security firm UpGuard Inc. is at it again, finding another misconfigured file repository on the Amazon Web Services Inc. (AWS) cloud, this one exposing Verizon customer account data.
Because many internal Verizon account PINs were available, UpGuard said the exposed data could be used to let attackers take over customer accounts for nefarious purposes.
While Verizon data was leaked, the file repository was actually operated by a third-party partner, Israel-based NICE Systems Ltd., which reportedly parked Verizon call center data on a misconfigured S3 storage bucket left wide open to public access.
UpGuard apparently has a "Cyber Risk Team" tasked with searching for such cloud-based vulnerabilities. The company, which made the Verizon discovery last month and reported it this week, earlier found that personal information about millions of U.S. voters was left exposed on a simililarly misconfigured S3 data store (see "AWS S3 Misconfiguration Leaks Personal Info of Nearly 200 Million Voters").
While no criminal activity has been connected to the exposed data in recently reported cases -- the fault of user misconfigurations, not cloud platform flaws -- UpGuard said the Verizon info could be used by attackers to take over accounts for "SIM Swap" scams or to thwart two-factor authentication.
The Verizon case also serves to expose the risks of third-party vendors handling sensitive data about customers who have no idea how their personal information is being used, or by whom.
"The prospect of a host of your applications and digital accounts being compromised from one third-party vendor's exposure of data is not science fiction, but the unfortunate reality of cyber risk today," the company said in a post Wednesday. "The data exposed in the Verizon/NICE Systems cloud leak is, indeed, a testament to how profoundly every aspect of life today is touched by those systems to which we impart so much knowledge."
The case also adds to the growing list of cloud-based security vulnerabilities being reported by various companies. For examples:
UpGuard said Verizon confirmed the data exposure, which reportedly claimed it affected 6 million customers.
Here's a summary of the Verizon case wrapped up in a handy infographic:
 [Click on image for larger view.]
The Verizon Data Leak (source: UpGuard)
[Click on image for larger view.]
The Verizon Data Leak (source: UpGuard)
About the Author
David Ramel is an editor and writer at Converge 360.